By Evan Grey Legal Contributor, SatNews
The commercial space industry has crossed a critical threshold. For years, the sector theorized about the eventual weaponization of the orbital domain and the legal vulnerabilities of dual-use satellite architectures. As of early March 2026, those theories are being tested over Iran — not in some future scenario, but now. We are no longer anticipating the application of the Law of Armed Conflict (LOAC) to space; we are watching military commanders interpret it in real-time.
The joint U.S.-Israeli military campaign launched against Iranian infrastructure on February 28, known as Operation Epic Fury, provides an unprecedented look at how modern space powers navigate the legal boundaries of orbital warfare. The tactical admissions by U.S. defense officials regarding electronic warfare, coupled with the actions of commercial proxy satellite operators supplying data to Tehran, are fundamentally straining the definitions of “combatant,” “armed attack,” and “civilian object” under international law.
The Legal Anatomy of Multi-Domain Non-Kinetic Warfare
The operational reality of modern conflict dictates that space and cyber commands act as the vanguard. On March 2, Chairman of the Joint Chiefs of Staff Gen. Dan Caine explicitly confirmed that U.S. Space Command and U.S. Cyber Command acted as “first movers” in the strikes on Iran. Gen. Caine noted that forces began by “layering non-kinetic effects” to disrupt and degrade Iran’s sensor and communication networks, effectively blinding the adversary’s early warning systems before the first kinetic munitions were fired.
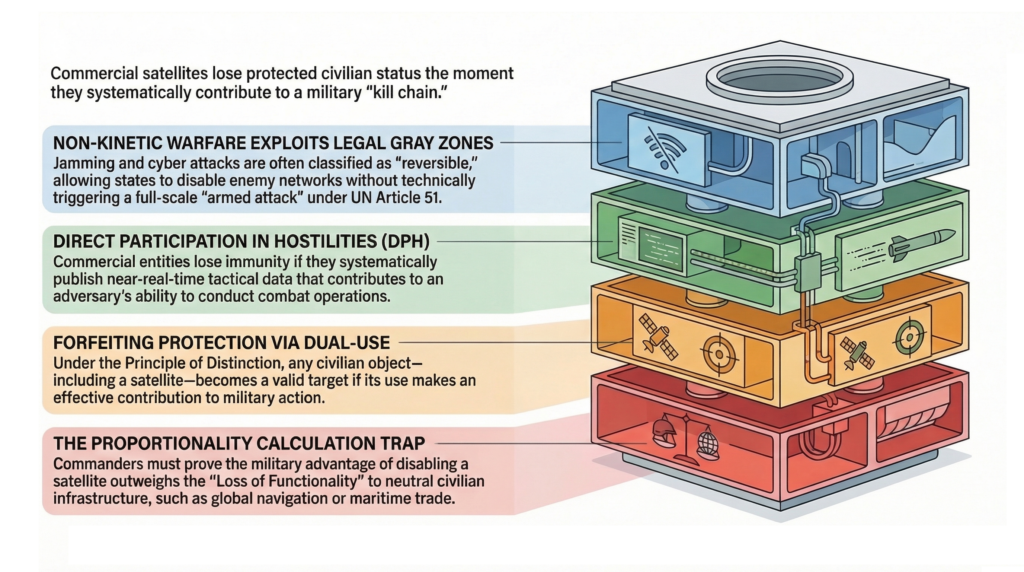
From a legal perspective, this reliance on multi-domain non-kinetic effects — where U.S. Cyber Command exploits terrestrial ground networks while Space Command executes targeted uplink and downlink jamming of Iranian and proxy satellite systems — is not just a tactical preference. It is a highly calibrated legal strategy designed to exploit a distinct gray zone within international law.
The legal architecture here is deliberate. Under international law, an “armed attack” triggering Article 51 self-defense rights generally requires severe physical destruction or loss of life. RF jamming and cyber disruptions are temporary, reversible, and cause no permanent hardware damage — they arguably never cross that threshold. Yet jamming a neutral state’s satellite still conflicts with ITU regulations prohibiting “harmful interference” and the Outer Space Treaty’s mandate for peaceful use. State militaries increasingly rely on electromagnetic and cyber warfare precisely because it lets them operate in this gap — achieving vital tactical objectives without triggering the legal tripwires of kinetic escalation.
The Commercial Proxy: The MizarVision Precedent
This legal framework becomes far more complex when commercial entities enter the battlespace. Iran is developing its domestic “Martyr Soleimani” low-earth orbit constellation, but the program remains nascent. To fill the intelligence gap, Tehran relies on foreign commercial infrastructure.
In recent weeks, Chinese commercial geospatial intelligence firms, notably MizarVision, have begun publishing highly annotated, high-resolution imagery of U.S. and allied assets across the Middle East. Distributed under the guise of open-source intelligence, MizarVision has released granular imagery of U.S. aircraft deployments at bases in Saudi Arabia, force buildups in Diego Garcia, and Patriot missile batteries in Bahrain. This data effectively serves as a proxy Intelligence, Surveillance, and Reconnaissance (ISR) feed for Iranian forces and their regional affiliates.
A critical distinction: MizarVision does not operate its own satellites. According to Hu Bo, Director of the South China Sea Probing Initiative at Peking University, the high-resolution imagery MizarVision circulated was sourced from U.S. and European commercial providers — specifically Vantor (formerly Maxar Intelligence) at approximately 0.3-meter resolution and Planet Labs for wide-swath maritime imagery. A MizarVision representative confirmed the company sources imagery from “diverse” providers including Western commercial entities. What MizarVision contributed was not access to Chinese reconnaissance assets but AI-driven object detection, annotation, change tracking over time, and theatrical repackaging for Weibo and X distribution.
This provenance makes the legal question far more complex than a simple state-versus-state confrontation. The satellites capturing the imagery are American. The company annotating and weaponizing the output is Chinese. The beneficiary of the intelligence is Iranian. The traditional LOAC framework, built around bilateral conflict between clearly defined parties, was not designed for this kind of transnational data supply chain.
The OSINT Loophole and Direct Participation in Hostilities (DPH)
The MizarVision precedent exposes a significant and not fully tested loophole in international space law: the weaponization of the public domain. MizarVision is not transmitting covert, encrypted telemetry directly to Iranian command centers. Instead, they are publishing annotated imagery of U.S. stealth fighters and Patriot batteries on public social media networks like X and Weibo. By claiming these products are simply “Open-Source Intelligence” (OSINT) available to the global public, the operator attempts to maintain plausible deniability.
However, as The Woomera Manual on the International Law of Military Space Operations (Oxford, 2024) highlights, the orbital domain severely lacks established State practice. Because space law remains notoriously underdeveloped, military legal scholars must frequently extrapolate from the maritime domain. Under the established Updated Newport Manual on the Law of Naval Warfare, a civilian merchant vessel enjoys protection from attack, unless it “is integrated into the enemy’s intelligence network” or uses its radio to transmit tactical fleet movements. Once it does, it exposes itself to targeting. MizarVision publishing annotated OSINT imagery of U.S. bases operates on an analogous trajectory — not as a satellite operator, but as the intelligence intermediary that transforms raw commercial data into actionable military products.
Section 5.8.3 of the DoD Law of War Manual defines “Direct Participation in Hostilities” (DPH) explicitly. Civilian entities that take a direct part in hostilities lose their immunity from attack. The manual’s language is broad: DPH includes actions that “effectively and substantially contribute to an adversary’s ability to conduct or sustain combat operations.”
The standard relies on the systematic nature of the disclosures. A single, isolated social media post by a civilian news agency does not constitute an act of war. However, if a commercial operator systematically publishes near-real-time tactical data that effectively completes a belligerent’s kill chain, the fact that it publishes the data “publicly” may not preserve its civilian immunity. The temporal proximity of this sustained data campaign to kinetic operations increases the likelihood that adversarial commanders will classify the action as Direct Participation in Hostilities through Constructive Military Contribution.
The Principle of Distinction and the Proportionality Trap
The most significant implication of Operation Epic Fury may be the active testing of the Principle of Distinction (Additional Protocol I, Article 52). A commercial satellite is a protected civilian object by default. Under the dual-use exception, it risks losing that protection if its use makes an effective contribution to military action.
In July 2023, the Department of Defense revised Section 5.4.3.2 of its Law of War Manual, reversing its prior position on the presumption of civilian status. Decision-makers must now presume persons or objects are protected unless available information indicates they are military objectives — a presumption that serves as the starting point for a commander’s good-faith judgment. When a commercial entity systematically disseminates granular targeting data, commanders operating under this framework may assess that the entity has forfeited its civilian protections.
Crucially, any response against such dual-use commercial infrastructure is still governed by the principle of Proportionality. A kinetic anti-satellite missile strike that creates thousands of pieces of indiscriminate orbital debris would undeniably violate LOAC. Yet, non-kinetic attacks present a complex Proportionality Trap — one that the MizarVision case makes uniquely tangled.
In the standard dual-use scenario, military legal scholars rely on the “Loss of Functionality” standard. If U.S. Space Command jams a dual-use constellation that is used 10% for military targeting but 90% for global civilian maritime navigation, commanders are required to calculate the downstream loss of functionality to civilian infrastructure. Blinding that satellite may not cause physical shrapnel, but it carries a measurable risk of economic or navigational harm to neutral third parties.
But MizarVision introduces a layer the standard framework never anticipated. The satellites providing the raw imagery are American — operated by Vantor and Planet Labs, serving thousands of legitimate commercial, scientific, and governmental customers worldwide. The entity weaponizing the data is a Chinese firm with no orbital assets of its own. Jamming or degrading U.S.-operated commercial satellites to deny MizarVision access would simultaneously deny service to every other customer of those constellations — an act of self-inflicted collateral damage with no precedent in LOAC. The alternative — targeting MizarVision’s terrestrial data processing and distribution infrastructure in China — raises an entirely different set of sovereignty and escalation questions. Space Command must navigate a proportionality calculus for which no existing doctrine was written.
A New Legal Baseline for Commercial Operators
Operation Epic Fury has made one thing clear: the commercial space economy is not insulated from terrestrial conflict. Satellite operators need to adjust their risk calculus now, while these doctrines are still being written.
A common counter-argument: Western companies routinely publish battlefield imagery, seemingly exposing them to the same targeting risks as MizarVision. U.S. state practice actively mitigates this exposure through Regulatory Geofencing. During the Ukraine conflict, the U.S. government restricted Ukrainian access to commercial imagery via platforms like the Global Enhanced GEOINT Delivery (GEGD) system, and it continues to strictly enforce limits on imagery resolution over Israel. By actively restricting commercial feeds during conflicts, the U.S. aims to prevent its commercial sector from crossing the DPH threshold. Conversely, by allowing MizarVision to operate without such restraints, Beijing is increasing the jurisdictional exposure of its commercial assets — even when those assets are, in this case, the annotation layer rather than the orbital hardware.
The absolute legal distinction between civilian commerce and military infrastructure is increasingly conditional. The MizarVision precedent makes the new boundary clear: the threat to commercial operators is not limited to those who own satellites; it extends to any entity in the data supply chain that transforms commercial imagery into military-grade intelligence. And the exposure runs both directions. Operators who voluntarily entangle their analytical products in active kill chains cannot rely on ambiguous civilian protections — but neither can the upstream satellite operators whose data feeds are weaponized without their consent. The legal exposure ripples through every node in the chain, from orbit to annotation desk to social media post.
About the Author
Evan Grey is a legal contributor for SatNews. A lawyer with a focus on regulatory policy and international relations, he specializes in the evolving geopolitical and industrial frameworks of the global space sector.


